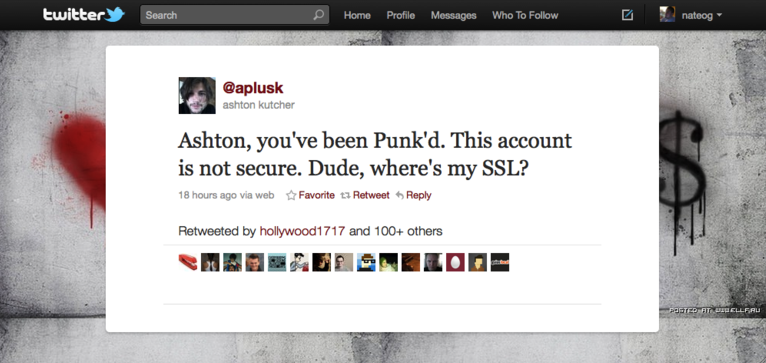
The hacking of Ashton Kutcher’s Twitter account on 2 March 2011 is an uncommonly tangible example of a Cybersecurity breach. He fell victim to a preventable vulnerability when on a public WiFi network. Kutcher was lucky to be infiltrated by education-focussed, ‘white-hat’ hackers with an ironic disposition. Their message to his 6,399,074 followers, “Ashton, you’ve been Punk’d. This account is not secure. Dude, where’s my SSL?” was for them to keep their own accounts safe through the use of Secure Sockets Layer protection. The hacking was intended as a simple reminder that, for most people, computer security is something of a ‘known unknown’, and is why internet security companies like Symantec (the makers of Norton Antivirus) are thriving right now.
On 16 February, Symantec launched the world’s first Cybercrime Index & Tools in London, citing £1.9 billion as the projected cost of online crime to the British economy for 2011. The Norton dashboard for the index provides a good range of insights. On Friday March 4th, the Norton Cybercrime index was 13% higher than the previous day. We’re told in their news section that an unidentified Australian online cosmetics company lost details from 1,000 credit card numbers, (including names and addresses,) to hackers. We’re also informed that 78% of identity theft occurs through hacking, whilst 21% is accidental. And their tip of the day? Take care when giving apps on social media websites access to your account because some social networks now also hold phone numbers and addresses.
For the Australian government that sort of educational information is a key component of the Cyber Security Strategy they launched on 23 November 2009. Their portfolio of education initiatives includes last year’s National Cybersecurity awareness week; the Staysmartonline website and alert service; and the Budd:e education modules. On a policy level, their objectives are that all Australians – individuals, corporations and government agencies – be aware of cyber risks and secure their computers. Like the hackers into Kutcher’s Twitter account, the government wants us all to take steps to protect our identities, privacy and finances online – and protect our comrades, customers and constituents as well.
Backing up these objectives Australia now has a Cyber Security Policy and Coordination (CSPC) Committee, run by the Attorney General’s department; a national Computer Emergency Response Team (CERT); and a Cyber Security Operation Centre (CSOC). These departments range in scope from partnerships with business, through to cyber warfare capability in the event of a serious threat to national security.
Introduced in December 2010, the Australian Internet Service Provider’s voluntary code of practise, iCode, exemplifies government-business co-operation. Its central assumption is that ISPs and consumers “can and must share responsibility for minimising the risks inherent in using the internet”. By monitoring their networks for signs of problematic activity, (such as the seeding of a virus, or unknown participation in a botnet,) the ISPs will either alert customers via email or phone calls or quarantine them to offline cul-de-sacs on their systems. This is surveillance in the name of the national interest, and it indicates that computer hygiene is becoming mandatory for all netizens.
But without doubt, the most astonishing glimpse of a new era of Cybersecurity is the Stuxnet worm. In February 2011, Symantec released another report which added to speculation that this worm is a highly funded military operation (possibly from the U.S. or Israel). The capabilities of Stuxnet include infiltrating Iran more than any other country (60% of instances); transferring itself into their secure nuclear facility via a USB stick; recording what normal operations look like; and then replaying that normal-looking behaviour to the monitoring screens – whilst exploiting Windows WinCC software running on Siemens controllers to then wreck the centrifuges unhindered. If the U.S. and Israel are indeed behind it, it is an ingenious alternative to fighter planes and bombing civilians, but it also sets the precedent of anonymous warfare. And it is possible for the public to protest against a physical act of war, but it’s hard to say anything other than “Wow!” when it comes to this weapon.
The implications from all this are clear: if we are to live in what the Australian government calls The Digital Economy, full of smart grids controlling our transport, energy and utilities, with tightly integrated supply chain management; and if there are cyber-criminals who’re looking for easy vulnerabilities; then there’s no room for an innocent computer user who could unwittingly take part in a Denial Of Service attack. It is in our personal, professional and public interest to smarten up… while maintaining a careful eye on restrictions to our civil liberties.

Scott David leads User Experience strategy and design at the World Economic Forum, across their digital platforms for data-driven knowledge and communities of global leadership.